Modern backup strategies often follow the 3-2-1-1-0 rule, but implementation varies widely.
Two environments can claim compliance with 3-2-1-1-0 and deliver very different resilience outcomes.
The difference is architecture design — specifically copy count, media diversity, and isolation between tiers.
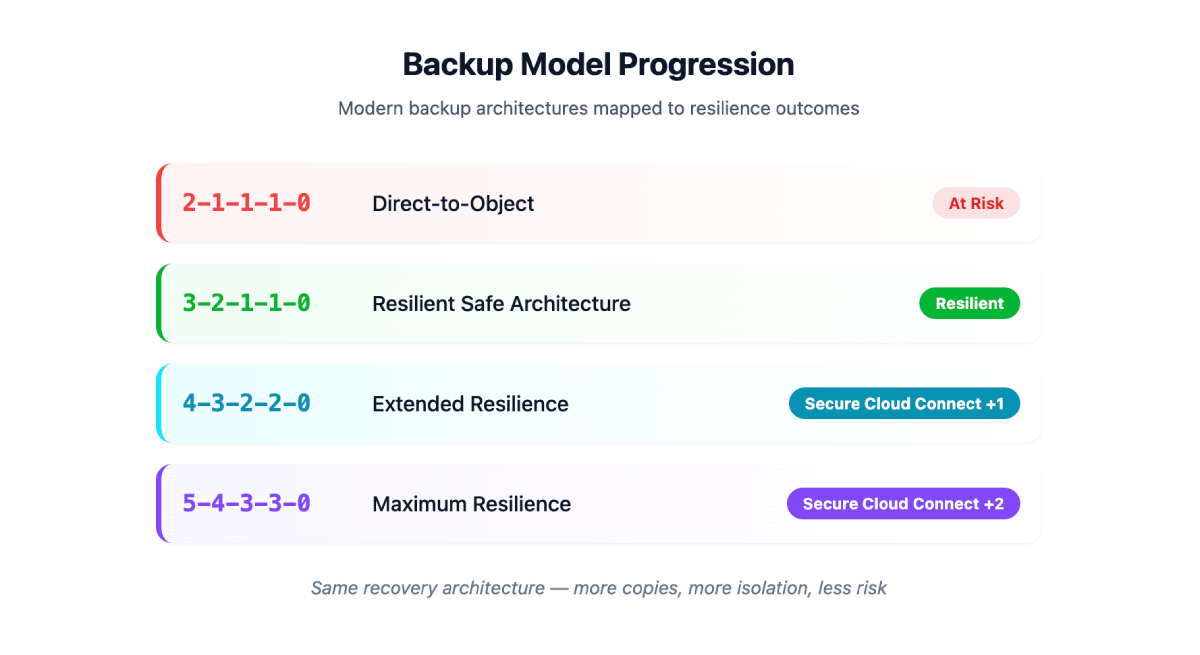
As architectures progress from direct-to-object storage to isolated Cloud Connect tiers and redundant offsite copies, resilience increases in measurable ways:
- More independent copies
- Greater isolation between control plane and backup data
- Reduced blast radius during ransomware events
The backup architecture progression model below maps common MSP backup architectures to their actual resilience outcomes.
Understanding the 3-2-1-1-0 “Zip Code” Rule
Veeam popularized the modern 3-2-1-1-0 rule for backup resilience:
- 3 copies of your data
- 2 different types of media
- 1 offsite copy
- 1 air-gapped or immutable copy
- 0 backup errors verified through testing
The models below show how MSP architectures compare — and how increasing those numbers increases availability and decreases risk.
MODEL 1 – Direct-to-Object Backup (2-1-1-1-0)
At Risk
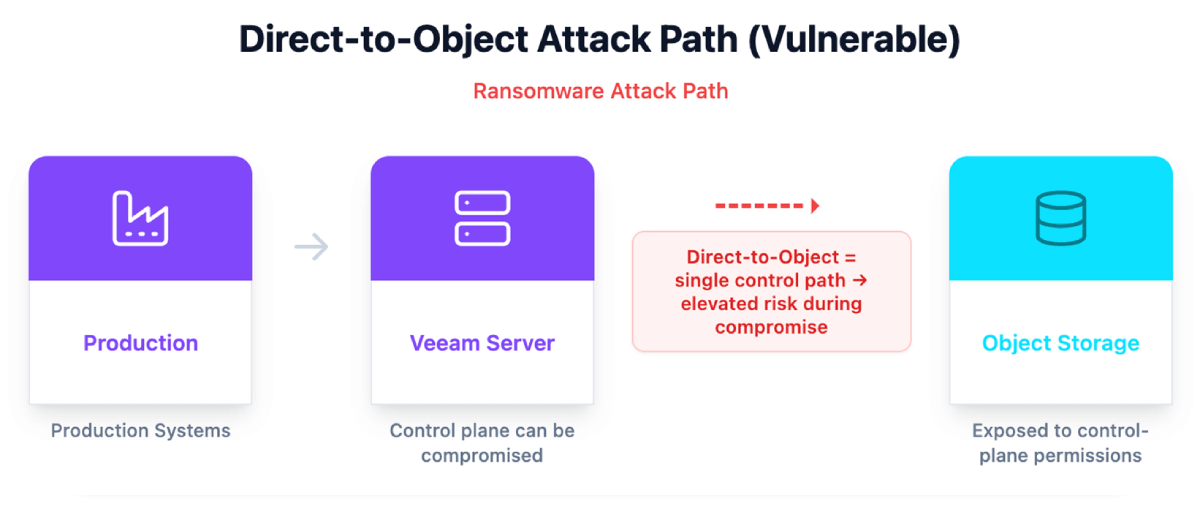
Most small Veeam environments today operate at this level.
What this means:
- 2 total copies (production + object storage)
- 1 type of backup media
- 1 offsite copy
- 1 immutable layer
- 0 verified errors (assumed)
Risk profile:
This model depends entirely on the Veeam control plane. If the Veeam server is compromised, attackers can target object storage via exposed credentials or API delete permissions.
It provides offsite storage – but not true isolation.
Cloud Connect: The Isolation Boundary
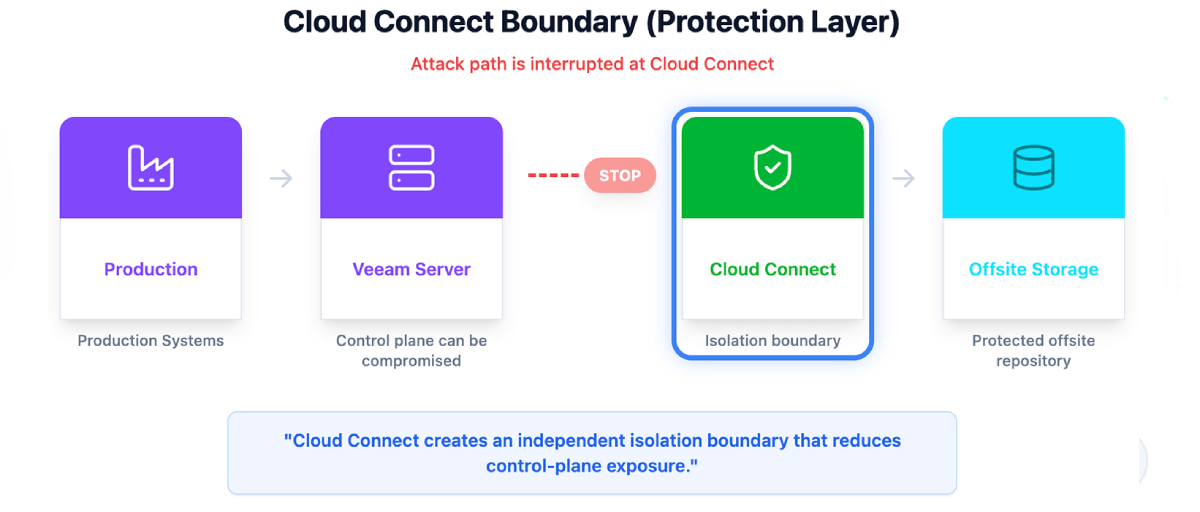
Cloud Connect introduces an independent isolation boundary.
It interrupts the ransomware attack path before it reaches offsite storage.
Even if the Veeam server is compromised, attackers cannot directly issue destructive commands to the Cloud Connect target.
This isolation layer is what transforms basic backup into resilient backup architecture.
MODEL 2 – Baseline Safe Architecture (3-2-1-1-0)
Resilient
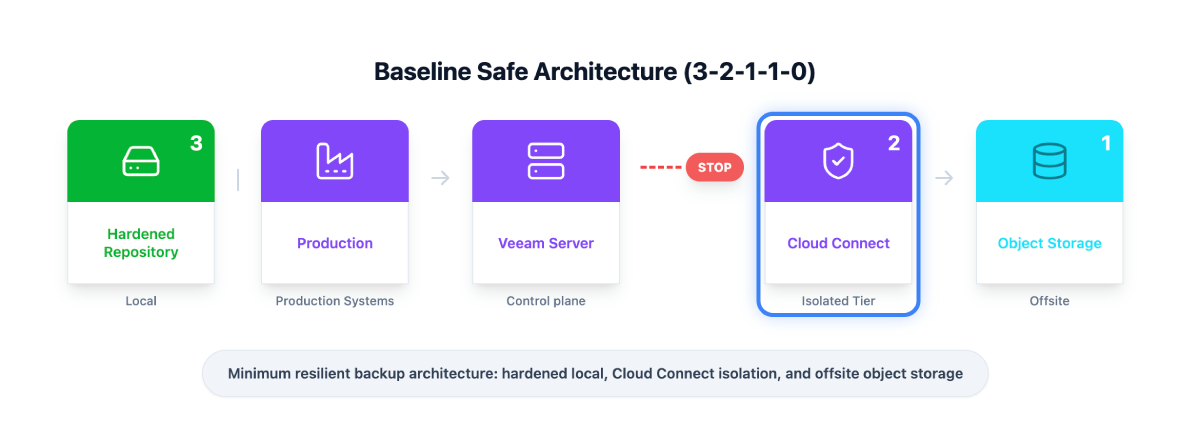
This model increases the first two numbers in the zip code:
From 2-1-1-1-0
To 3-2-1-1-0
What changed:
- +1 total copy (now 3 total copies)
- +1 media type (hardened repository + object storage)
Architecture:
- Production data
- Local immutable hardened repository
- Secure Cloud Connect isolation
- Offsite object storage
This is the modern minimum MSP baseline.
It provides:
- Local immutability
- Offsite protection
- Isolation boundary
- Reduced control-plane exposure
Risk decreases.
Availability increases.
MODEL 3 — Extended Resilience (4-3-2-2-0)
Secure Cloud Connect +1
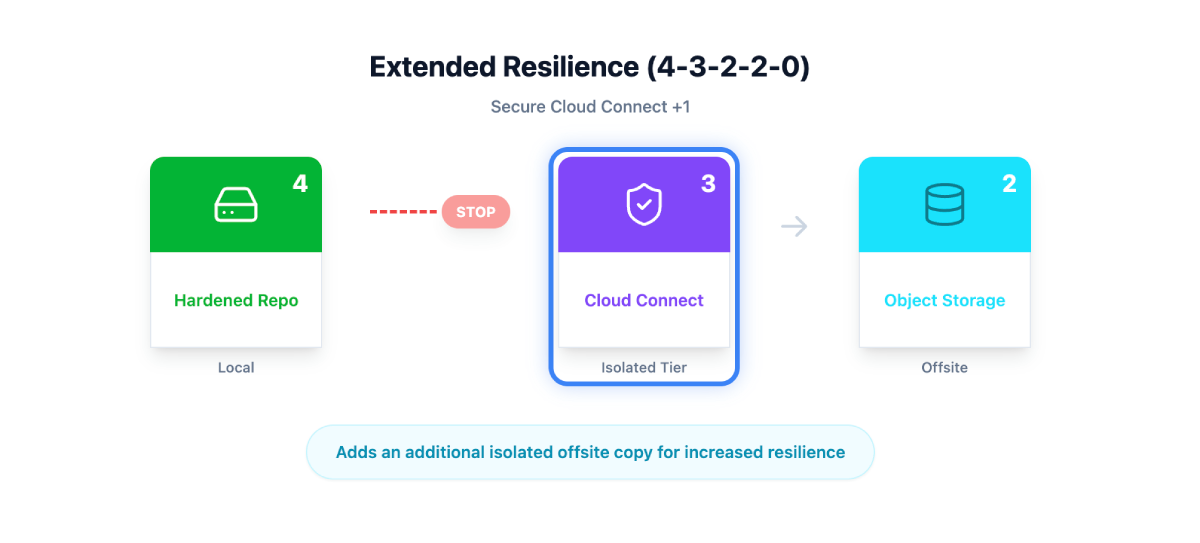
This model increases the first four numbers by one:
From 3-2-1-1-0
To 4-3-2-2-0
What changed:
- +1 total copy (now 4 copies including production)
- +1 media type
- +1 additional offsite copy
- +1 additional air-gapped layer
This creates:
- 4 total copies of data
- 3 different media types
- 2 offsite copies
- 2 air-gapped / isolated layers
The recovery architecture remains the same.
What increases is redundancy and availability.
If one provider or repository is unavailable, another remains accessible.
MODEL 4 – Maximum Resilience (5-4-3-3-0)
Secure Cloud Connect +2
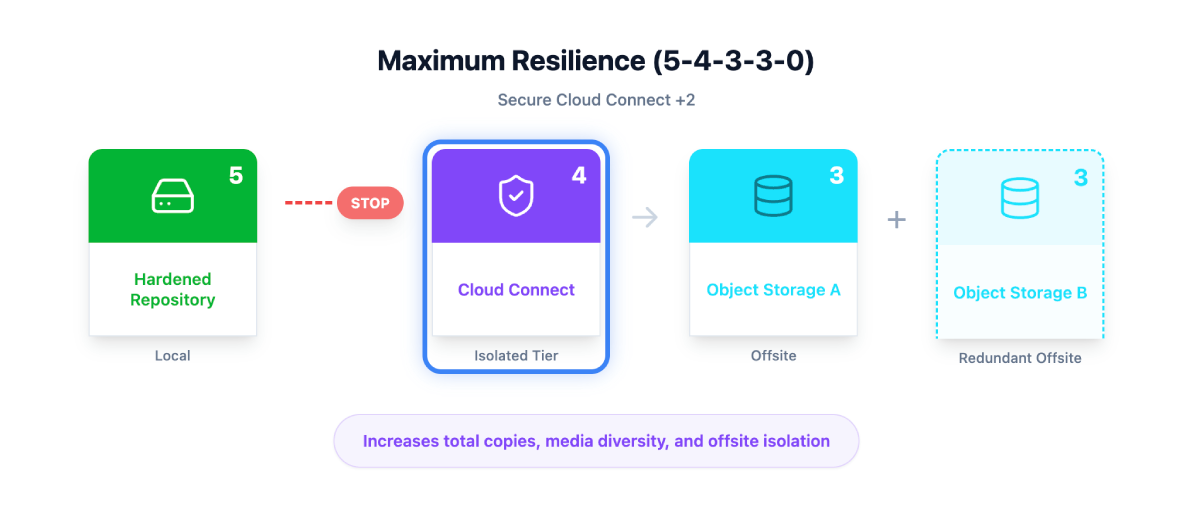
This model again increases the first four numbers by one:
From 4-3-2-2-0
To 5-4-3-3-0
What changed:
- +1 additional total copy (now 5 including production)
- +1 additional media type
- +1 additional offsite copy
- +1 additional air-gapped copy
This results in:
- 5 total copies of data
- 4 different media types
- 3 offsite copies
- 3 air-gapped / isolated layers
Backups are now distributed across multiple independent providers and storage locations.
Any single failure – provider outage, credential compromise, region issue – does not eliminate recoverability.
Availability increases again.
Risk decreases again.
What Actually Changes Between the Models
The recovery method does not change.
The isolation boundary does not change.
Cloud IBR can recover from any isolated backup source.
What changes is how many independent copies exist — and how exposed you are to single points of failure.
In simple terms:
- You are buying more availability
- You are reducing risk
- You are increasing recovery certainty
How MSPs Should Present This
- Start with the executive summary diagram.
- Explain the 3-2-1-1-0 rule in two sentences.
- Show how each model increases the first numbers in the zip code.
- Ask the customer:
How many copies of your backup do you want when ransomware hits?
Budget dictates which model makes sense.
But resilience always increases as copies and isolation increase.
Final Takeaway for MSPs
Backup tools are necessary.
Architecture determines recoverability.
Resilience does not come from adding more backup paths.
It comes from increasing isolation, increasing availability, and reducing single points of failure.
As you move from:
2-1-1-1-0 → 3-2-1-1-0 → 4-3-2-2-0 → 5-4-3-3-0
You are decreasing risk and increasing the certainty that recovery will succeed.
And ultimately:
Ransomware becomes an IT incident — not a business-ending event.
